今日最推
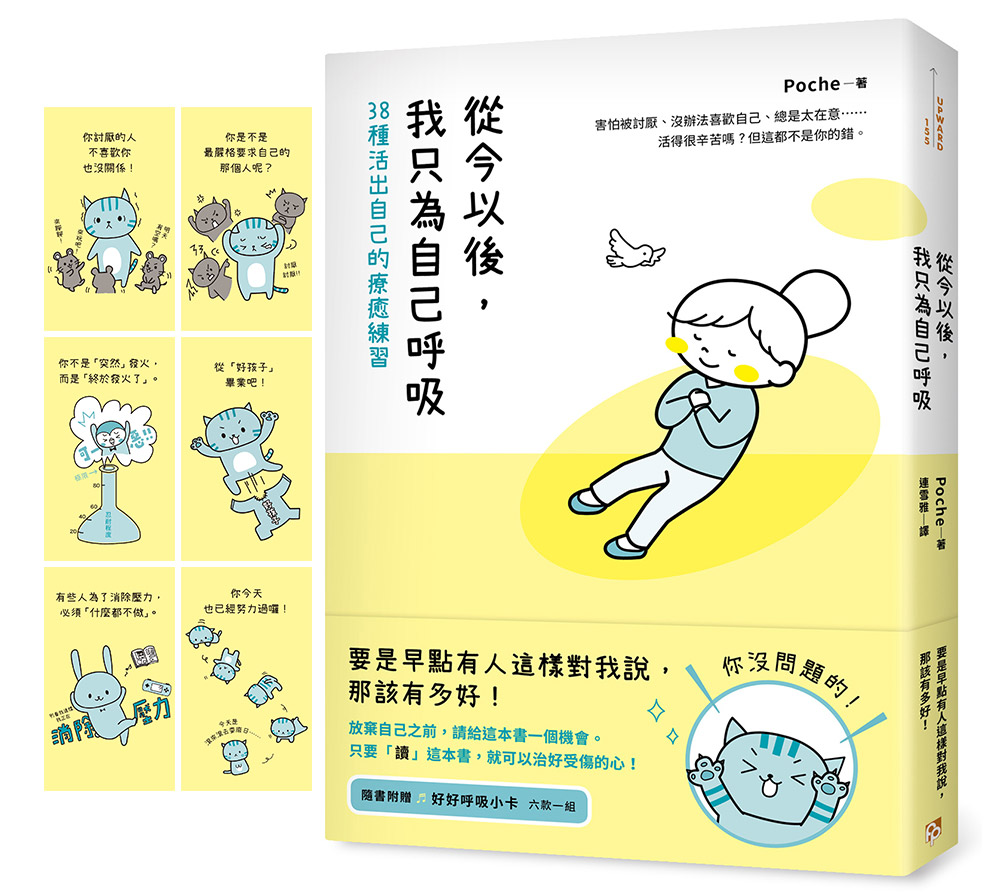
我可以覺得好累了嗎?|從今以後, 我只為自己呼吸: 38種活出自己的療癒練習
\你沒問題的!/
放棄自己之前,請給這本書一個機會。
只要「讀」這本書,就可以治好受傷的心!
【隨書附贈】
「好好呼吸小卡」六款一組
▌害怕被討厭、沒辦法喜歡自己、總是太在意……
▌活得很辛苦嗎?但這都不是你的錯。
(´;ω;`):「我可以覺得好累了嗎?」
沒有想被喜歡但也不想被討厭;遇到不舒服的事總被說是想太多;有很多該做的事卻提不起勁,連平常喜歡的事都不想做了……或許是我不夠好?是不是我不夠努力?當陷入煩惱的死胡同,有時候,你只想停止呼吸。
人生很難,這個人不喜歡你、那個人老是生氣、就算盡全力,還是得不到認同……但「那又如何」?就算全世界都在指責你,這也根本不是你的錯,你唯一的錯,是你太溫柔了,不溫柔的人不會有的煩惱,才會找上你。
本書收錄日本超熱門諮商師Poche的38則短篇,只要開始讀,就能擺脫焦慮、得到療癒。從今天開始,試著只聽從內心的聲音,不去檢查TO DO LIST、不用和任何人說話、不勉強自己到外面散心,告別每天早上醒來就覺得好累的自己,從今以後都只為自己呼吸!
♥ 日本超熱門諮商師Poche於臺灣出版的第一本書
「希望閱讀本書後,一直以來深陷自責的你,能夠減少自責的次數。總是為了他人勞心勞力的你,今後請試著把時間和體力花在自己的身上。希望早上醒來就覺得『好累……』的你,往後的每一天都可以過得輕鬆些。更重要的是,希望本書能夠成為讓你『察覺』如何活得輕鬆的契機。」——本書作者/Poche
♥ 有沒有可能,錯的並不是你
☹「明明已經盡全力了,卻達不到要求。」
→那個要求是不是「1+1=3」?錯誤的公式怎麼努力都不會對!
☹「好後悔!我那時候為什麼不罵他!」
→你沒有生氣,是因為當時的情況並不適合。相信你的判斷,不需要自責!
☹「還是好討厭自己……」
→你為什麼要喜歡自己?不用一定要喜歡自己,「不那麼討厭自己」就好了!
♥ 更舒坦的人生,大可「不必」
✓不必改變自己,請想一想,對方有重要到值得讓你改變自己嗎?
✓不必費心去迎合對方,比起被你討厭的人討厭,「被喜歡」才更麻煩。
✓不必對自己那麼嚴格。對自己親切,不會造成別人的困擾。
✓不必每件事都親力而為,即使你做得到,也沒人規定你非做不可。
✓不必為了消除壓力而做什麼,試著「什麼都不做」吧!
♥ 當你能「察覺」到壓力,就已經離「消除壓力」不遠了
Poche開設的診所,網路和面談諮商經常排到好幾個月之後,為了能照顧到更多有煩惱的人,他開始在社群網站上發文,並挑選其中迴響熱烈的文章收錄成書。快被壓力壓垮的你,還請輕鬆地翻開這本書,從哪一頁讀都沒關係,只讀一兩句也可以。Poche的一字一句會像你身邊的空氣那麼自然,讓你能夠重新找回自在呼吸的方式!
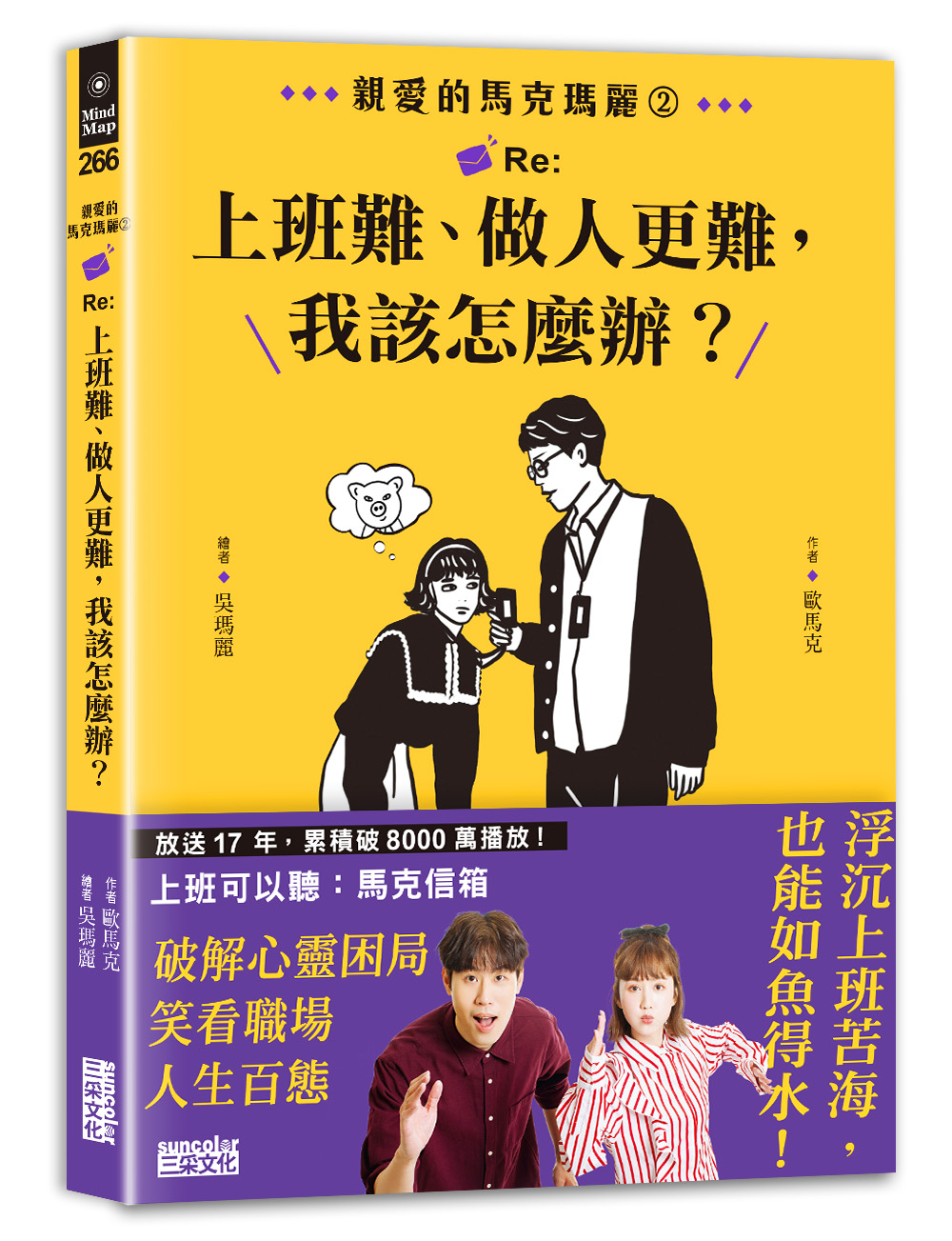
消滅社畜的23道陰影|親愛的馬克瑪麗 2 Re: 上班難、做人更難, 我該怎麼辦?
工作煩惱100%,都是因為「人」!
放送17年,累積破8千萬播放
◆馬克突破盲點,神開釋|瑪麗暗黑插畫,神意境◆
消滅社畜的23道陰影
不再當職場叢林的小白兔!
【暢銷佳績 得獎紀錄】
★2022博客來心理勵志百大
◤這些OS,你也有過嗎?◢
鳥事一大堆,精氣神被磨耗殆盡?
上班賣的是專業,還是尊嚴?
不過是一份薪水,非得如此心累?
不想當躺平族,但也不想當砲灰!
18歲那年成為靠聲音吃飯的男人,從打工仔到CEO,歐馬克打臉過人、也被現實打臉。
超過二十年的職場觀察後,他說:「沒有固定的同事、客戶多元、工作浮動多變,也許是未來世界的常態。」
不管你在什麼公司,什麼產業,只要通透「職場之道」,你就能心平氣和,風生水起,創造自己想要的生活方式。
《馬克信箱》從數千封來函海選,精煉23道生存必修題,為你開光點睛,從今以後找到理想生活。
★職場求生→解題專區★
▌工作一定要往上爬?
>>>時間不斷往前,未來一直來一直來,有成長的人可以更有餘裕地面對人生,而選擇停在原地的人,就會被時代給拋下。
▲想要過什麼樣的人生,決定在什麼時候停止成長,都是你的選擇。
▌為何到處都有暢秋的老屁股?
>>>你要想的不是他為什麼不會這些事情,而是他為什麼會在這裡。這個世界真正在運作的,是那些背後看不見的「道」。
▲觀察環境中一切細微的互動,找到自己的生存之道,你會更如魚得水。
▌為何拚命了,卻還是失敗!
>>>努力本來就有可能不會得到你想要的東西,但如果因此不去努力,那你就太傻了。
▲沒獲選不是失敗,你只是沒有被選到而已。
▌和討厭鬼共事好痛苦......
>>>我們沒辦法決定在工作場合遇到的人,如果不得已必須要與討人厭的人共事,戴上人格面具可以確保我們維持專業、避免衝突。
▲上班最重要的事情就是把事情做完做好,然後拿錢走人。
▌工作總是做不久……
>>>使用「求職評估表」把對工作的想像描繪出來,利用追問法,對自己進行靈魂拷問並排序,可以幫助你非常快速地篩選工作。
▲你相信什麼,你就會過著怎樣的人生。
不論現在的你有多痛苦,自覺關關難過、關關過不了,都不用灰心。
你現在以為的結果不是真的結果,只有當你認為一切都結束了,那才會變成真的結果。
Q:何時才能等到結果呢?
A:當你死的時候。
只要還有呼吸,還有心跳,每一個瞬間都是過程。
★馬克語錄→破解陰影★
〆想要遇到職場貴人,請先當那個可愛的人。
〆努力,是一種可支配的運氣。
〆職場上有很多的不順與不開心,來自於你搞錯了你為什麼在這裡。
〆你若要當蓮花,就得學會排解那些自命清高的苦。
從此浮沉上班苦海,也能如魚得水;
破解心靈困局,笑看職場人生百態!
全球獨家精裝典藏版|有用之人: 阿諾史瓦辛格改變命運、養成不敗意志的人生7律 (全球獨家精裝典藏版)
從身無分文的美國移民到眾望所歸,
卸下健美之神、傳奇巨星、政治人物光輝,
阿諾.史瓦辛格將 78 年奮鬥淬鍊為 7 大原則,
帶領迷茫之人站穩腳跟、挺過風浪,實現有意義的人生!
★《紐約時報》NO. 1 暢銷書
★ 英國亞馬遜「2023 年度百大暢銷書」
★ 誠品外文館「編輯推薦選書」
★ 出版前,火速售出 28 國版權
★ 美國亞馬遜編輯精選「2023 年度最佳書籍」,連續 6 週總榜 TOP 20
★ 阿諾.史瓦辛格唯一繁體中文著作,硬漢精神掀起全新勵志風潮
他,曾是背包裡僅有 200 塊錢的美國移民,
一步步練成橫掃大獎的健美之神、跨世代傳奇巨星、斜槓政壇的加州州長。
走過無人看好的荊棘之路,阿諾到過低谷,承受常人難以想像的肉體與心靈疼痛,
始終堅守父親的唯一教誨───「成為有用之人」,持續回饋世界。
► 找到使命、仰望自我、鍛鍊毅力、校正心態、面對挫敗、選擇聽眾、練習回饋 ◄
7 大原則,開啟阿諾.史瓦辛格的人生坦途,今後也將改變你的一生!
#擁有明確的願景、清晰的圖像,也別忘了照照鏡子
青少年時期,阿諾只是憧憬美國的一切,金門大橋、帝國大廈、肌肉海灘……
直到在健美雜誌封面上看見當時的環球先生兼演員雷格.帕克,通往美國的路才變得清晰。
他看到自己手持冠軍獎盃,受群眾景仰,而一旦「看到」,就能「做到」。
#沒有 B 計劃!既然要做,就豁出去做
1987 年,阿諾已然成為好萊塢最具代表性的動作片演員,不過接下來,他想演喜劇。
沒有人看好這個想法,媒體一片唱衰,最後在他的堅持和縝密計劃之下,
獲得環球公司總裁支持,打造出票房破億的喜劇片《龍兄鼠地》。
#百分之百值得追求的目標,絕對需要百分之百的努力
身為健美運動員,阿諾每天鍛鍊 5 個小時,持續 15 年。
為了演出《魔鬼終結者》,他練習射擊的次數之多,以至能蒙眼完成每一場槍戲。
擔任公職後,他親力親為,坐鎮指揮現場,一夜完成數十萬人的安置、救護工作。
#想讓自己成為暢銷商品,先搞清楚要向誰推銷
阿諾在候選人辯論會初登場,就面臨大批質疑:又是健美選手,又是演員,可靠嗎?
但他抓住對手銳利的提問,將其化為向選民推銷的語言,
最終在選舉拿下 48.6% 得票率,三年後更以高達 55.9% 得票率連任加州州長。
#屈服於負面情緒,就等於讓它偷走你的時間
2018 年,阿諾因心臟瓣膜置換意外進行開胸手術,術後被迫停工、停止重訓。
在連呼吸都有灼燒感的處境下,他將負面情緒「換檔」,
最後只在加護病房待了六天,便如期回歸片場拍攝《魔鬼終結者:黑暗宿命》。
#你懂的不如你以為的多,所以閉上嘴巴,打開胸懷
穿梭於父親、運動員、演員、政治人物等多重身分中,阿諾始終認為,世界就是最好的教室。
於是,他把握每一次跟健身同伴閒聊的時刻,積極向達賴喇嘛、戈巴契夫等各界人士請益。
事實證明,好奇心和謙卑不僅為他帶來人脈,還有隨時可以運用的知識力量。
#人生不是零和博弈,你付出越多,往往得到越多
與健友互相監督動作,演員之間不吝指教,無償培訓特殊奧運舉重選手,
打破「以我為重」這面鏡子後,阿諾開始看見需要幫助的人,
同時也領悟到,回饋賦予生命意義,最終引導他成為「有用之人」。
唯有成為對自己、對這個世界有用的人,人生才有改變的可能。
知彼知己:AI思考方式|How AI Thinks: How We Built It, How It Can Help Us, and How We Can Control It
知彼知己:AI思考方式【How AI Thinks: How We Built It, How It Can Help Us, and How We Can Control It】✰解密 AI 思維,掌握未來契機
AI正在改變我們的生活,理解 AI 的思維方式,將成為迎接未來巨變的關鍵!奈傑爾•圖恩(Nigel Toon) ——人工智慧(Artificial Intelligence)領域的專家,為你揭開AI學習與思考的奧秘!以往,我們認為計算機不過是高級運算機器,擅長儲存訊息,進行象棋等邏輯遊戲的對弈。但是,最近這幾年,AI已經進步到能夠像人類一樣思考,曾經的「搜尋引擎」正在進化為「答案引擎」,並且以驚人的速度,顛覆著教育、醫療,甚至藝術、創意等諸多領域。然而,AI 如何理解情感和語境?它又如何在博弈遊戲中取得勝利?最重要的是,我們如何與 AI 協作,共同創造超越人類認知的洞見和創新?例如瞬間編寫程式,或者解開蛋白質的3D結構難題。本書將帶你探索AI的思維過程,展示AI如何創造前所未見的影像,或使用各種語言進行溝通。本書不僅是探索AI人工智慧的窗口,也是重新認識人類思維的鑰匙!
'Nigel Toon is a visionary leader in the field of artificial intelligence... a must-read for anyone who wants to understand the past, present and future of artificial intelligence' Marc Tremblay, Distinguished Engineer, Microsoft
Those who understand how AI thinks are about to win big.
We are used to thinking of computers as being a step up from calculators - very good at storing information, and maybe even at playing a logical game like chess. But up to now they haven't been able to think in ways that are intuitive, or respond to questions as a human might. All that has changed, dramatically, in the past few years.
Our search engines are becoming answer engines. Artificial intelligence is already revolutionising sectors from education to healthcare to the creative arts. But how does an AI understand sentiment or context? How does it play and win games that have an almost infinite number of moves? And how can we work with AI to produce insights and innovations that are beyond human capacity, from writing code in an instant to unfolding the elaborate 3D puzzles of proteins?
We stand at the brink of a historic change that will disrupt society and at the same time create enormous opportunities for those who understand how AI thinks. Nigel Toon shows how we train AI to train itself, so that it can paint images that have never existed before or converse in any language. In doing so he reveals the strange and fascinating ways that humans think, too, as we learn how to live in a world shared by machine intelligences of our own creation.
一場海外職場大冒險|離開舒適圈之後, 抵達成熟之前: 一場奇幻的海外職場大冒險
●11萬粉絲引頸期待!耶魯大學高材生帶你一窺法國、日本、香港、美國不可言說的職場文化!
●圖文作家&Podcast主持人 Vito大叔、資深日本顧問 福澤喬、T1籃球大聯盟副會長 劉奕成 齊聲推薦
在法國,找工作時讓面試官一見鍾情,勝過擁有超完美履歷;
在日本,讀懂空氣是職場求生的必備技能;
在香港,加班加好加滿是日常,享受生活才是奢侈;
在美國,向上管理比展現實力更重要……
踏出巴黎高等商學院及耶魯大學校門後,作者Jeff C.一腳闖進外資金融圈的殘酷世界,遊走於法國、日本、香港、美國各地,見識到各種光怪陸離的現象,也經歷了冷暖自知的人性考驗,深刻體悟到:路,不一定是人走出來的,也可能是野獸隨時會出沒的地方。人生處處是風險,置身詭譎多變的職場猶如野外求生,不能盲目地前進,唯有保持清醒,才能活到最後。
職場人生就像參加一場登高賽,跳脫舒適圈是成長必須付出的代價。從青春到世故,走過十年的探索之路,下一場未知的旅程才正要開始……
「我想將過去十年間發生的一切記錄下來,讓閱讀這些故事的人能夠體驗那些對我來說非常珍貴的瞬間:有歡笑、溫暖,也有寂寞,以及一點點的傷感。」 —— Jeff C.
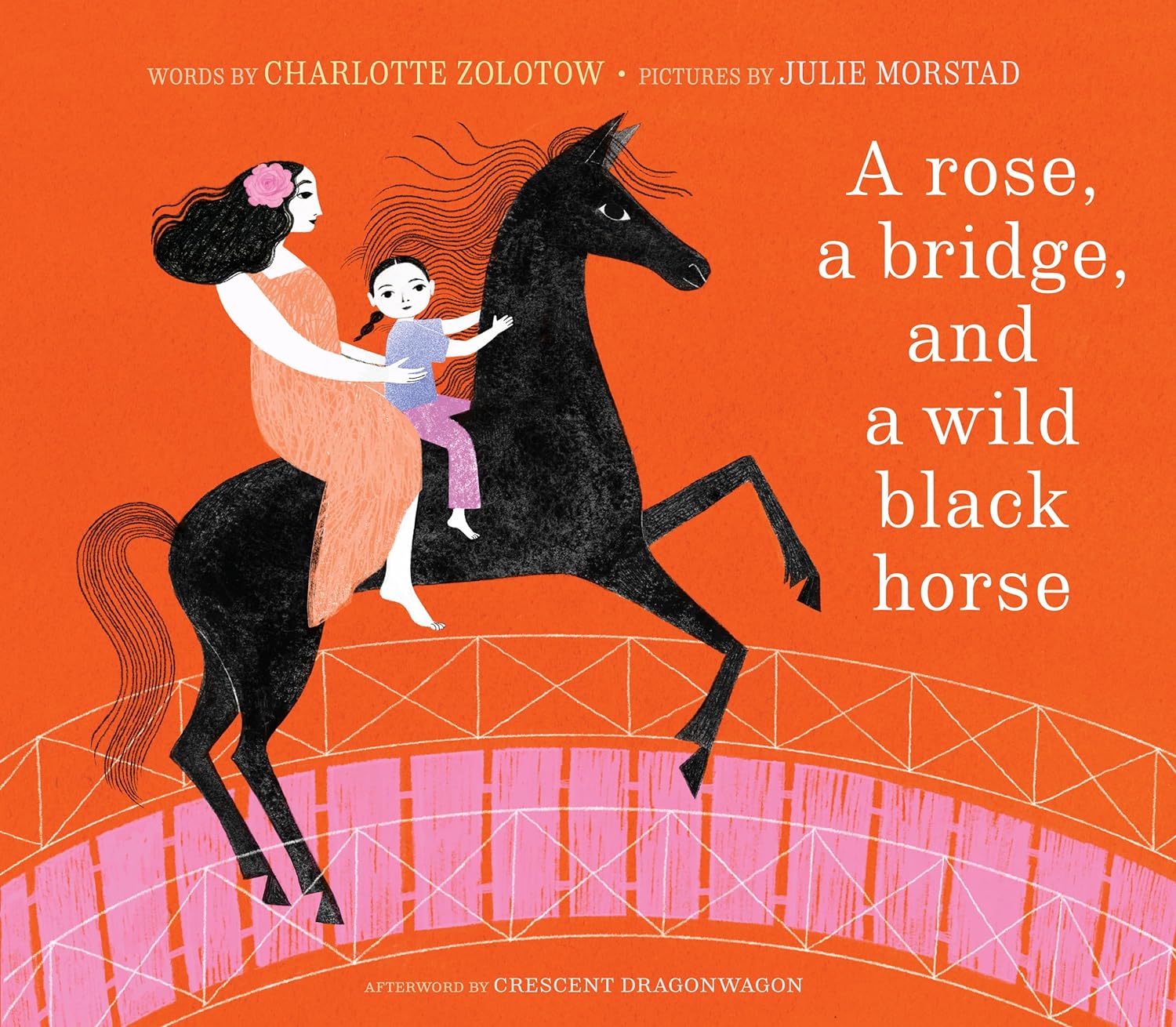
獻給媽媽的愛的宣言|A Rose, a Bridge, and a Wild Black Horse
一個女孩宣布長大後她將為母親做的所有事情——從爬山、游泳跨越海洋,到採摘最粉紅色的玫瑰,到建造最大的橋樑和一座城堡供母親居住,馴服一匹野黑馬供她母親騎——最後她將帶著她的朋友在環遊世界時陪伴她。本書最初出版於 1964 年,是兒童文學作家夏洛特·佐洛托(Charlotte Zolotow) 深受喜愛的作品,而今由她的女兒、著名作家Crescent Dragonwagon 重新構思,並由獲獎藝術家Julie Morstad 繪製插圖。
好康優惠
新書報到 | 馬上選購
全球獨家精裝典藏版|有用之人: 阿諾史瓦辛格改變命運、養成不敗意志的人生7律 (全球獨家精裝典藏版)
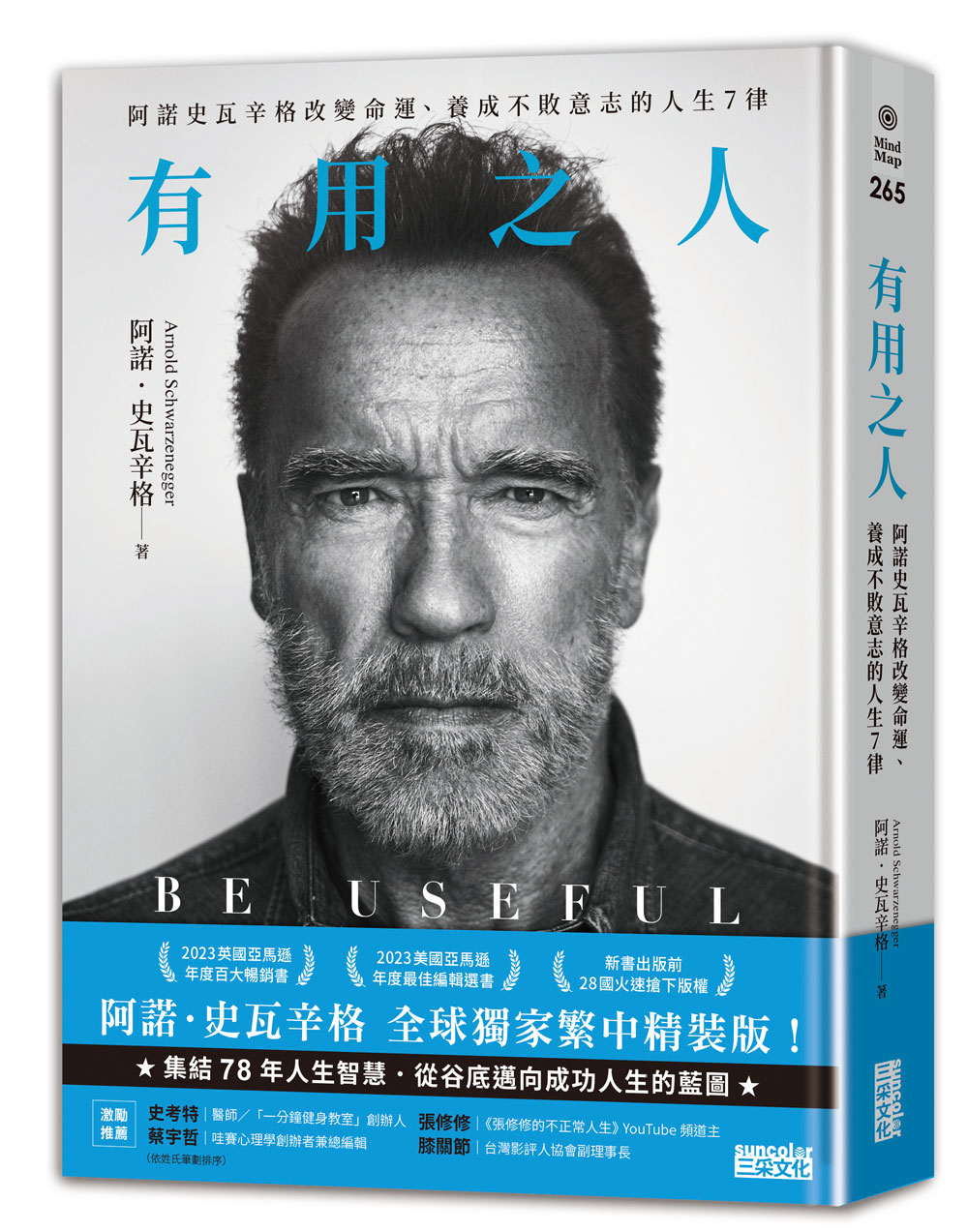
從身無分文的美國移民到眾望所歸,
卸下健美之神、傳奇巨星、政治人物光輝,
阿諾.史瓦辛格將 78 年奮鬥淬鍊為 7 大原則,
帶領迷茫之人站穩腳跟、挺過風浪,實現有意義的人生!
★《紐約時報》NO. 1 暢銷書
★ 英國亞馬遜「2023 年度百大暢銷書」
★ 誠品外文館「編輯推薦選書」
★ 出版前,火速售出 28 國版權
★ 美國亞馬遜編輯精選「2023 年度最佳書籍」,連續 6 週總榜 TOP 20
★ 阿諾.史瓦辛格唯一繁體中文著作,硬漢精神掀起全新勵志風潮
他,曾是背包裡僅有 200 塊錢的美國移民,
一步步練成橫掃大獎的健美之神、跨世代傳奇巨星、斜槓政壇的加州州長。
走過無人看好的荊棘之路,阿諾到過低谷,承受常人難以想像的肉體與心靈疼痛,
始終堅守父親的唯一教誨───「成為有用之人」,持續回饋世界。
► 找到使命、仰望自我、鍛鍊毅力、校正心態、面對挫敗、選擇聽眾、練習回饋 ◄
7 大原則,開啟阿諾.史瓦辛格的人生坦途,今後也將改變你的一生!
#擁有明確的願景、清晰的圖像,也別忘了照照鏡子
青少年時期,阿諾只是憧憬美國的一切,金門大橋、帝國大廈、肌肉海灘……
直到在健美雜誌封面上看見當時的環球先生兼演員雷格.帕克,通往美國的路才變得清晰。
他看到自己手持冠軍獎盃,受群眾景仰,而一旦「看到」,就能「做到」。
#沒有 B 計劃!既然要做,就豁出去做
1987 年,阿諾已然成為好萊塢最具代表性的動作片演員,不過接下來,他想演喜劇。
沒有人看好這個想法,媒體一片唱衰,最後在他的堅持和縝密計劃之下,
獲得環球公司總裁支持,打造出票房破億的喜劇片《龍兄鼠地》。
#百分之百值得追求的目標,絕對需要百分之百的努力
身為健美運動員,阿諾每天鍛鍊 5 個小時,持續 15 年。
為了演出《魔鬼終結者》,他練習射擊的次數之多,以至能蒙眼完成每一場槍戲。
擔任公職後,他親力親為,坐鎮指揮現場,一夜完成數十萬人的安置、救護工作。
#想讓自己成為暢銷商品,先搞清楚要向誰推銷
阿諾在候選人辯論會初登場,就面臨大批質疑:又是健美選手,又是演員,可靠嗎?
但他抓住對手銳利的提問,將其化為向選民推銷的語言,
最終在選舉拿下 48.6% 得票率,三年後更以高達 55.9% 得票率連任加州州長。
#屈服於負面情緒,就等於讓它偷走你的時間
2018 年,阿諾因心臟瓣膜置換意外進行開胸手術,術後被迫停工、停止重訓。
在連呼吸都有灼燒感的處境下,他將負面情緒「換檔」,
最後只在加護病房待了六天,便如期回歸片場拍攝《魔鬼終結者:黑暗宿命》。
#你懂的不如你以為的多,所以閉上嘴巴,打開胸懷
穿梭於父親、運動員、演員、政治人物等多重身分中,阿諾始終認為,世界就是最好的教室。
於是,他把握每一次跟健身同伴閒聊的時刻,積極向達賴喇嘛、戈巴契夫等各界人士請益。
事實證明,好奇心和謙卑不僅為他帶來人脈,還有隨時可以運用的知識力量。
#人生不是零和博弈,你付出越多,往往得到越多
與健友互相監督動作,演員之間不吝指教,無償培訓特殊奧運舉重選手,
打破「以我為重」這面鏡子後,阿諾開始看見需要幫助的人,
同時也領悟到,回饋賦予生命意義,最終引導他成為「有用之人」。
唯有成為對自己、對這個世界有用的人,人生才有改變的可能。
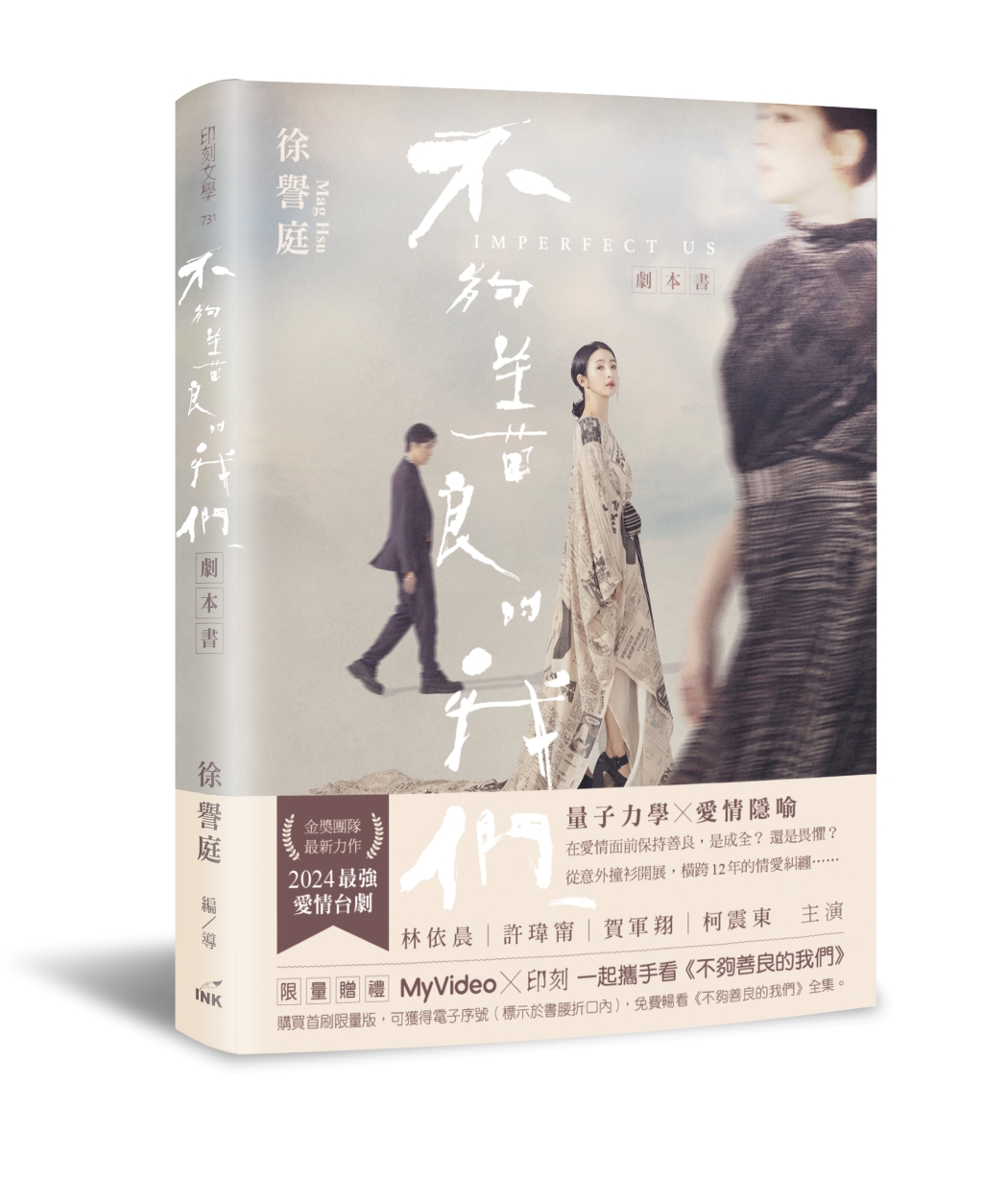
限量贈看片兌換碼|不夠善良的我們劇本書 (攜手看劇版/附贈MyVideo電子兌換序號)
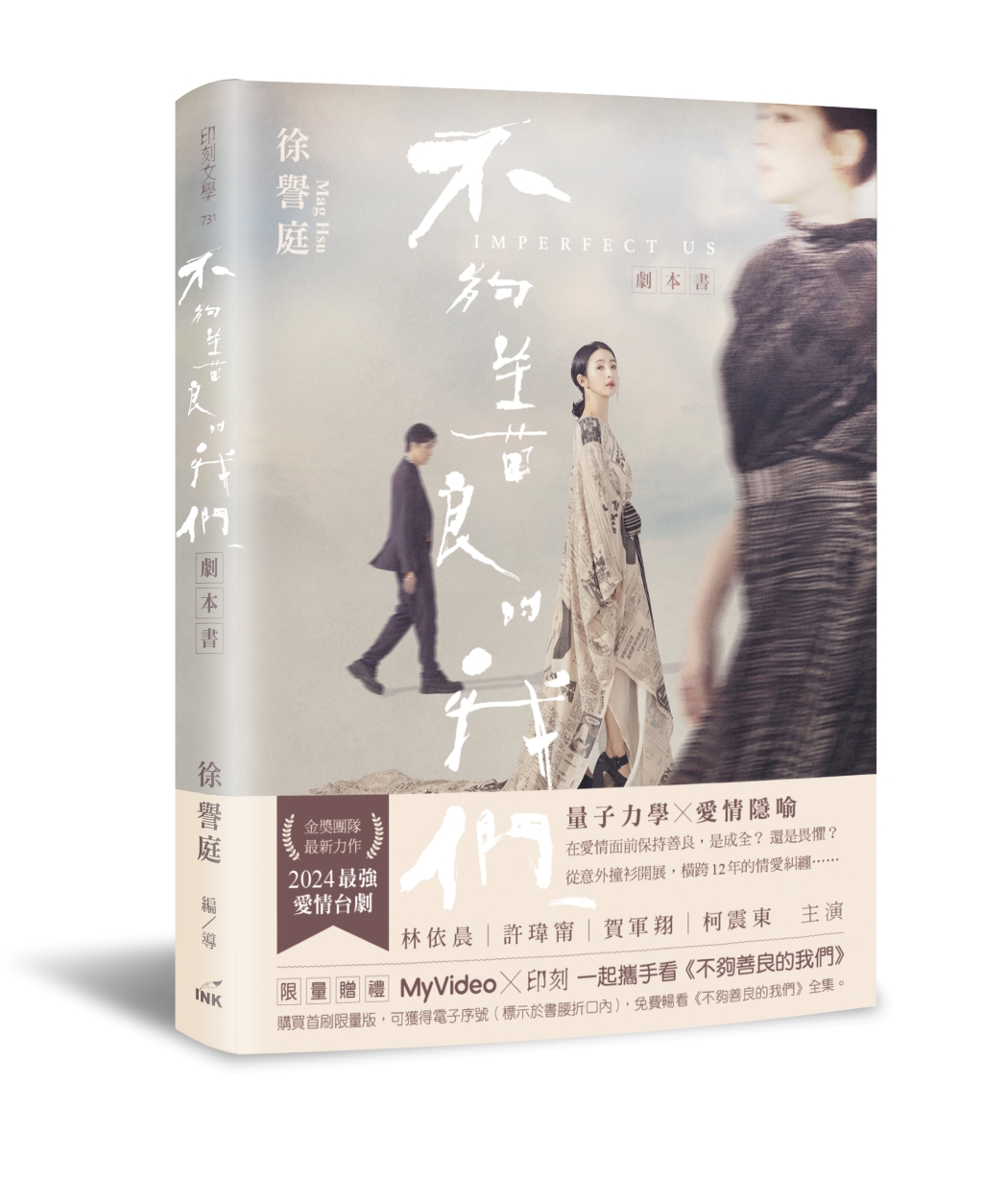
量子力學X愛情隱喻
在愛情面前保持善良,是成全?還是畏懼?
從意外撞衫開展,橫跨12年的情愛糾纏……
金獎團隊最新力作 2024最強愛情台劇
林依晨|許瑋甯|賀軍翔|柯震東 主演
‧耗時一年打造劇本,完整收錄八集創作,及編寫心路歷程
‧搭配精彩劇照與幕後工作影像
‧人氣編導+黃金演員卡司,詮釋愛情裡的小心機,訴盡婚姻裡諸多無奈
--
我們為人生定下了一個又一個的目標,為了成全那一個又一個很剎那的快樂,但你發現了嗎?其實大部分的時間,我們都活在痛苦裡。
四十不惑的簡慶芬很幸運的達到人生設定的目標──老公體貼、孩子聽話的幸福家庭。不過她卻發現,即使自己很努力的放大了微小幸福,但日子似乎只是千篇一律、日復一日,找不到下一個需要達成的目標。
沒有追求目標的痛苦,就失去了「痛快」。就這樣,她想起了一個人──當年被她打敗的情敵Rebecca,並在臉書上找到了她。
Rebecca的臉書貼文字數不多,從動態隱約得知她未婚、有個小鮮肉男友,生活充滿驚奇。但,那是「臉書上的她」。實際上的Rebecca,剛被房東通知要搬遷,時間被忙碌的工作填滿,成為屬下口中的「人生負面教材」。
這兩位從年輕時屢屢撞衫,又同天生日的女孩,如同「量子糾纏」般的她們又愛上同一個男人,展開了這場橫跨12年的愛恨情仇……
限量贈禮
MyVideo*印刻 一起攜手看《不夠善良的我們》
購買首刷限量版,可獲得MyVideo電子兌換序號(標示於書腰折口內,7 31前須兌換完畢),免費暢看《不夠善良的我們》全集。
《不夠善良的我們》MyVideo全集熱播>>https: twm5g.co D3bE
最新刊!|Kinfolk 51

Kinfolk第51期
【關於Kinfolk】2011年創立於波特蘭,Kinfolk 以其獨特審美和深刻生活理念,成為設計師、攝影師、廣告人及藝術家的靈感泉源。這份季刊,最初只是一個分享晚餐與聚會照片的部落格,在兩週內以超過200萬的點擊量,展現了它獨特的魅力和吸引力。Kinfolk 以其獨有的攝影風格與精緻排版聞名:人物不笑、時間仿佛靜止、綠植與餐桌的獨特視角,透過一種冷靜而克制,簡潔卻溫馨的美學,巧妙地詮釋了現代生活的精緻藝術。《Forbs》雜誌對其評價為“獨立雜誌的新聲音”,充分肯定了其在小眾出版界中的顯著成就。對於讀者而言,Kinfolk不只是一本雜誌,更是一種生活態度與風格的展現,代表了追求美好生活的不懈努力和獨到見解。
Since 2011 Kinfolk has established itself as a leader in art and culture, design and aesthetics, architecture, and homes and interiors. Our quarterly lifestyle magazine is sold in over 100 countries, published in three languages and makes the perfect coffee table magazine or gift for a creative. Featuring inspiring photography, fashion and style, as well as examinations of slow living, Kinfolk is an art and design publication that seeks to promote quality of life and connect a community of creative thinkers.
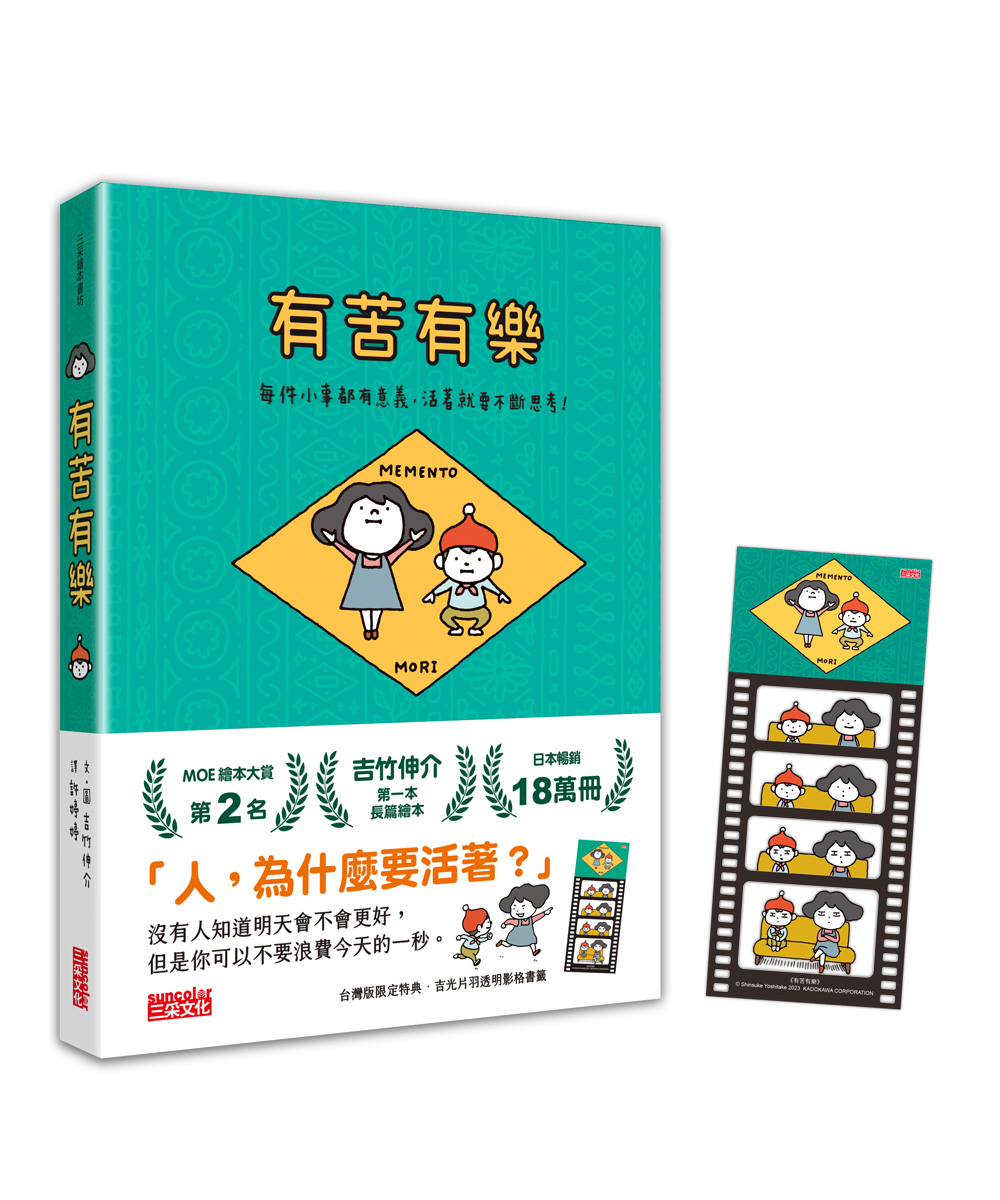
台灣版限定特典|有苦有樂: 每件小事都有意義, 活著就要不斷思考! (附吉光片羽透明影格書籤)
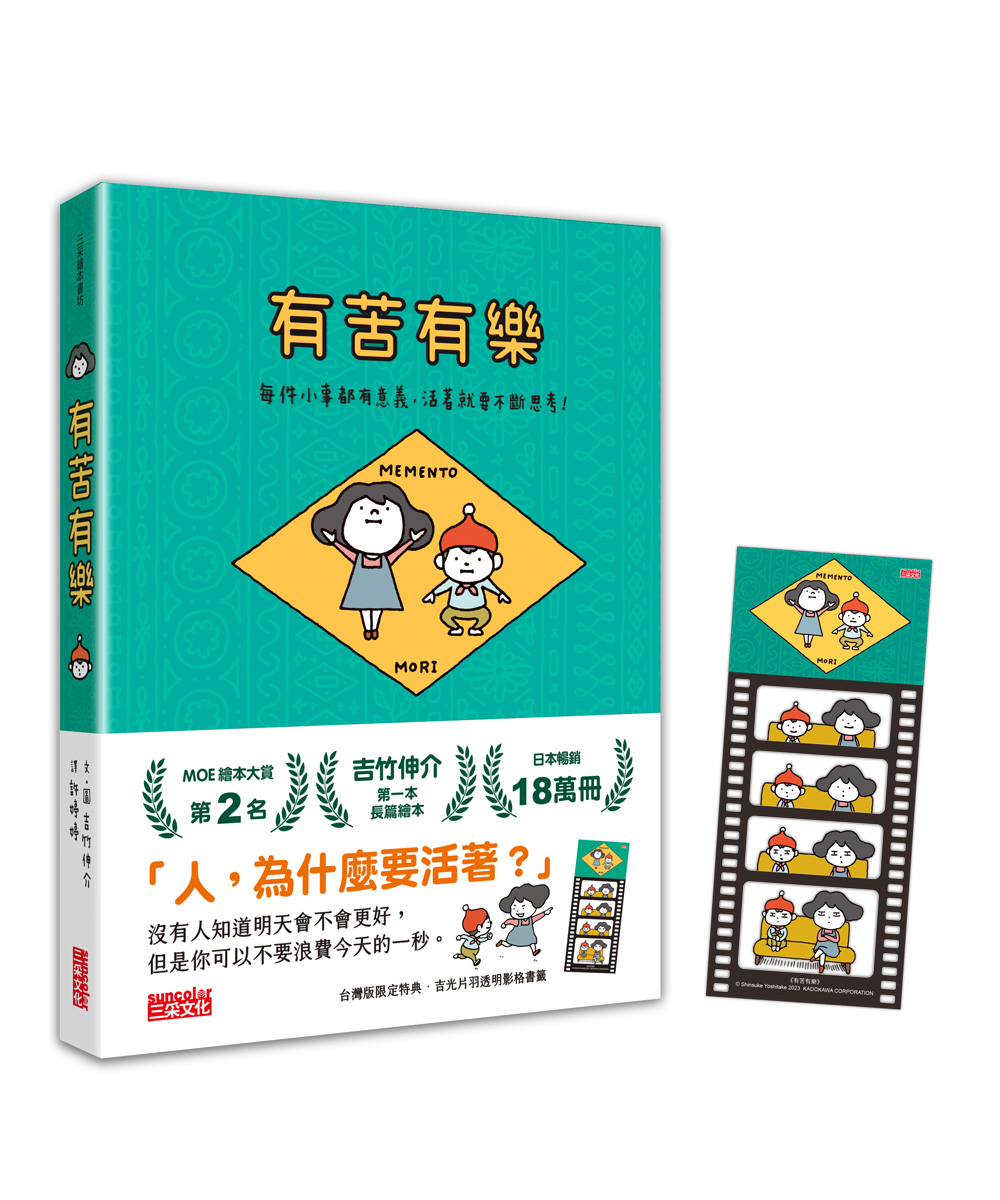
日本暢銷18萬冊
吉竹伸介第一本長篇繪本!
「人,為什麼要活著?」
人生啊,有苦也有樂,
沒人知道明天會不會更好,
但是你可以不要浪費今天的一秒。
★台灣版限定特典【吉光片羽透明影格書籤】
【國外暢銷佳績 得獎紀錄】
\榮獲各大日本繪本獎/
★2024年 紀伊國屋Kinobes!Kids 第1名
★2023年 MOE繪本大賞 第2名
★第11回 静岡書店大賞 兒童書新作部門 第2名
美妙的味道,是甜中帶有一點苦……
好看的故事,是笑中帶有一滴淚……
3篇小故事、3段童言童語,一起思考活著的意義。
1〈破掉的盤子〉
弟弟不小心打破姊姊手作的盤子……
弟弟覺得很抱歉,姊姊為什麼不在意?
珍貴的物品雖然想永久保存,
但世界上其實有更重要的東西……
2〈髒髒的雪人〉
雪人髒髒的,
它知道,只要冬天一結束,
自己就會融化消失,
於是開始自言自語……
我,為什麼存在這個世界上?
如果可以,有沒有別的選擇?
3〈無聊的電影〉
姊弟倆看完一部無聊的電影,
弟弟開始煩惱,如果以後的人生……
一直遇到無聊的事情怎麼辦?
這時,姊姊提出了不同的想法,
這個世界或許和人們想的不一樣喔!
【本書特色】
1.超人氣插畫家自寫自畫,用輕鬆的圖文思考生命的意義。
2.對日常小事有敏銳的觀察力,學習感受日常的每時每刻。
3.天馬行空的人生哲學,讓人意識到自己存在的價值。
【隨書好禮】吉光片羽透明影格書籤
★日本獨家授權★三采團隊精心設計★台灣版限定★
將書籤夾在任何頁面,任何筆記,
每個瞬間都變得閃閃發亮!
●尺寸:6.5X15公分
【書籍介紹】
◎有注音,8歲以下親子共讀,8歲以上自行閱讀。
◎六大領域分類:情緒、社會。
◎六大能力分類:表達溝通、關懷合作。
領券買書 | 閱讀推薦
町田苑香極治癒之作|即使你不在這裡 (親筆簽名版)

本屋大賞得主町田苑香寫給大人的極致治癒之作。
五篇關於離別之後的故事
無數個被溫柔牽起的瞬間。
如果難以想像遙遠的未來,請想起我。
我會在那裡等你,我知道你一定很努力。
所以放心地受傷,放心地生活,放心地前進吧。
◇ 守靈夜之夜
突然接到奶奶過世的消息,清陽暌違半年回到北九州的老家。
奶奶生前一直想看看孫女交往的對象,
但只要想到一喝醉就易怒的爸爸、沉迷拉霸機的媽媽、吵鬧的叔叔一家,
清陽就始終無法向男友介紹自己的家人……
◇ 阿婆進行曲
自從在前公司遭到霸凌和性騷擾,香子和別人相處都會感到害怕。
個性積極卻強硬的男友,希望她趕快找份「像樣」的工作,並計畫結婚。
我真的這麼差勁嗎?──香子不斷想著這個問題。
這時,她遇見每天都會在後院敲打大量碗盤杯壺的「交響樂阿婆」。
當香子向她搭話,阿婆竟說:
「妳也有吧。只要是停下腳步的人,都有想放在這裡的東西。」
◇ 黑洞
和我外遇的男人,拜託我做栗子澀皮煮給他太太吃。
我一顆一顆地剝著栗子皮,一邊想著我應該要和他分手才對。
有顆栗子被蟲蛀了一個小洞,照理說這種栗子要丟掉。
黑洞不斷冒出帶有澀味的浮渣,奶奶說這些浮渣都是壞東西。
噗咚。我把有黑洞的栗子裝進了給他的瓶子。
◇ 積雨雲誕生的時刻
我經常會在某個瞬間,突然什麼都不想要。這次的分手也是。
同一時間,我得知老家的藤江姑婆過世了。
意外的消息不只這個,藤江姑婆竟然是爺爺的情婦,
三十八年來,以「藤江」這個名字悄悄地在這裡生活著。
我跟著妹妹整理藤江姑婆的遺物,卻在不知不覺中梳理起至今的人生──
◇ 人生前輩
直到發現青梅竹馬藍生戀愛了,加代才意識到原來自己喜歡藍生。
更晴天霹靂的是,她無意間得知藍生很快就要搬家了。
焦躁的加代,打聽到藍生最近和一位叫作「死神婆子」的老太婆走得很近。
加代決定跟蹤藍生來到死神婆子的家。
沒想到,開門的竟是一位年輕迷人的女人……
◇
很多事物經過整理才能找得到,幸福也是。
於是才明白,原來幸福不必完美無缺,未必得克服一切。
也不只是一味灑脫或執著,而是放手要比緊握來得多。
每個充滿智慧的人生,都曾在迷惘與孤獨中跌撞。
那些無法如願的關係、無力解決的問題,他們走過,更比誰都感同身受。
讓他們擁抱你的踉蹌,憐愛你的傷痛。他們說不要緊,要聽進去。
原來也有一種幸福是,有人溫柔地向你保證——你會幸福的。
◇
他們也在這裡推薦
樂團|青虫aoi
作家|陳曉唯
作家|馮國瑄
作家|楊富閔
演員|簡嫚書
(依姓名筆畫序排列)
小說裡提出專業詞彙:「重啟症候群」,這樣的人就像游牧民族,必須不斷重啟生活。每當內心荒蕪的時候,必須再度離開,尋找水草豐美的棲息地,才能舒坦活下去。我好奇上網搜尋想了解更多,結果被小說家騙了,原來是小說家自創的詞彙,但我相信這只是一個還沒被廣受討論的議題。必須不斷歸零重新開始,才有辦法活下去。
我對這篇小說如此著迷,因為我也是這種人。
──作家.馮國瑄(摘錄自推薦序)
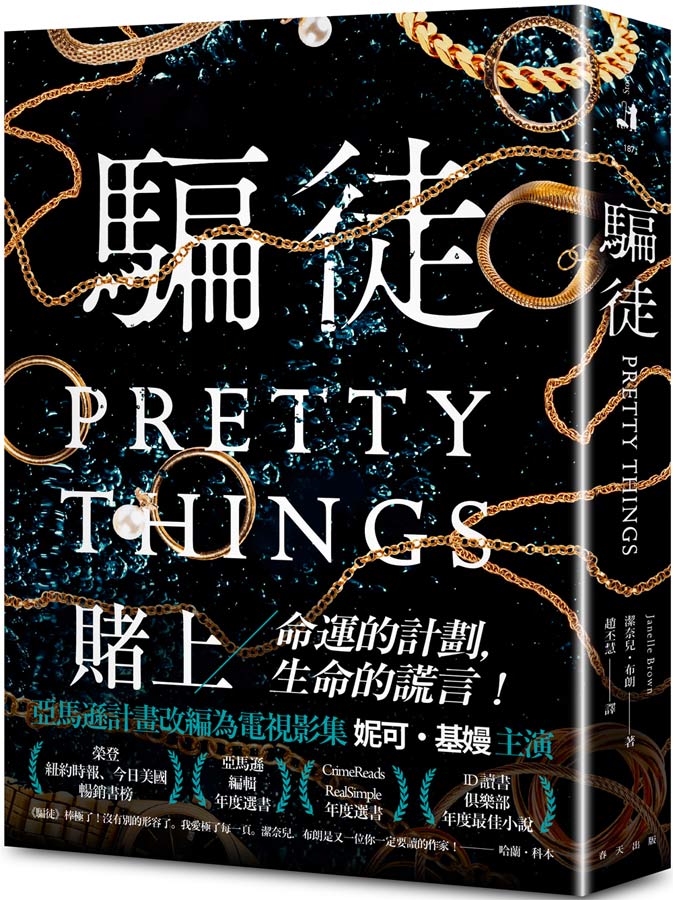
改編影集妮可基嫚主演|騙徒
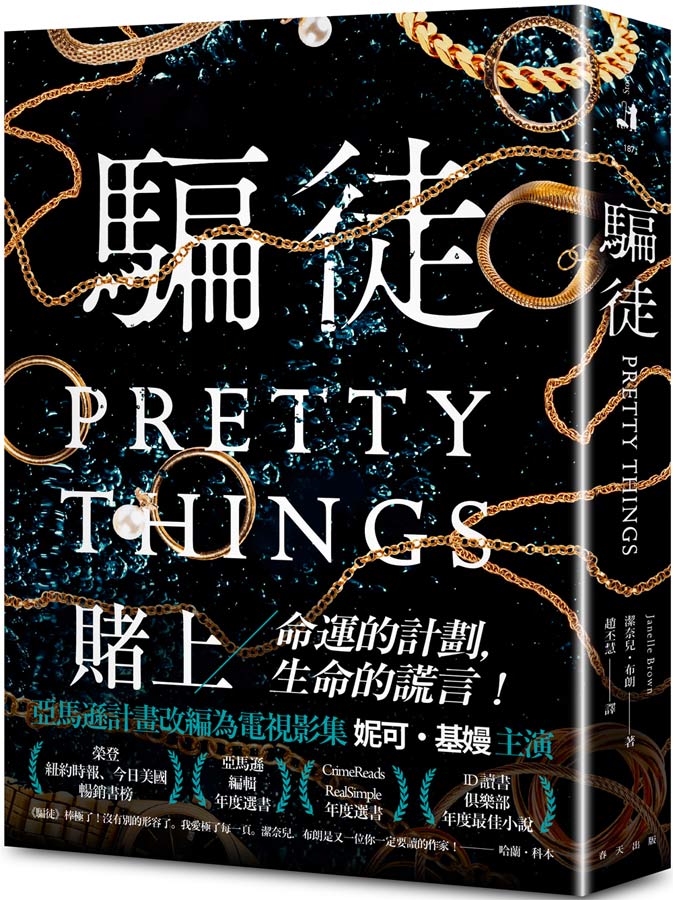
賭上命運的計劃,賭上生命的謊言!
亞馬遜計畫改編為電視影集 妮可.基嫚主演
.榮登紐約時報、今日美國暢銷書榜
.亞馬遜編輯年度選書
.CrimeReads 、RealSimple年度選書
.ID 讀書俱樂部年度最佳小說
窮困潦倒的騙子vs.權貴富有的名媛
兩名女子的慾望、嫉妒、復仇,引發畢生最大的騙局……
妮娜一度以為她的學歷能夠讓她有個發揮長才的事業,可是這個夢想破滅了。為了擺脫窮困生活,妮娜選擇承襲母親的專才──詐騙。因應母親天文數字般的醫藥費,她正在尋找目標中,這時妮娜想到了凡妮莎,一個上流社會的女繼承人,同時也是華麗而且人人羨慕的名媛。
十幾年前,兩人之間有著因為家人而糾結的秘密。
財富和慾望、嫉妒和憤怒,復仇心使然,妮娜決定展開她最危險的騙局──偽裝成新的身分,開始接近凡妮莎……
著名當代藝術家|KAWS: Family
【KAWS: Family】 ✰KAWS 粉絲必備收藏。KAWS,被視為當代的藝術巨擘,以其獨特的視覺語言和大型雕塑,席捲了藝術界、時尚圈與流行文化領域。他將街頭文化與流行藝術巧妙結合,顛覆了傳統藝術的疆界,為觀眾帶來耳目一新的視覺體驗。《KAWS: Family》 是 KAWS 首次於加拿大舉辦的大型個展,由多倫多安大略美術館主辦,本書收錄他過去二十多年的60多幅作品,涵蓋素描、繪畫、雕塑及精選商品,以及展覽現場照片、安大略美術館副館長兼首席策展人 Julian Cox 的文章,以及安大略美術館策展人兼總編輯 Jim Shedden 與 KAWS 的深度訪談。透過這些內容,讀者可以深入瞭解 KAWS 的創作脈絡,一窺他如何跨足於藝術、流行文化、產品設計與時尚等領域,發揮深遠的影響力。
American artist KAWS is one of the most famous living contemporary artists today. Renowned for his iconic visual language and larger-than-life sculptures, the artist draws on beloved pop culture icons to create a new and recognizable cast of characters of his own. The broad appeal of KAWS’ style has made his artwork accessible to collectors, museum visitors and the general public alike, and has led to collaborations with coveted global brands and immense commercial success.
KAWS: FAMILY, organized by the Art Gallery of Ontario, Toronto, marks the artist’s Canadian institutional exhibition debut with an array of his drawings, paintings, sculptures and selected products. The catalog features over 60 works from the past two decades, including installation photography; essays by Julian Cox, AGO Deputy Director and Chief Curator; and an interview with KAWS by Jim Shedden, AGO Curator of Special Projects and Director of Publishing. Together, this material provides new insights into KAWS’ influences and creative process as well as the impact his work has made across the spheres of fine art, pop culture, product design and fashion.
A graffiti artist since adolescence, Brian Donnelly (born 1974), known professionally by his moniker KAWS, received his BFA in illustration from New York’s School of Visual Arts in 1996. He has collaborated with brands such as Supreme, Nike and Comme des Garcons, and his work can be found in the collections of the High Museum of Art in Atlanta, the Modern Art Museum of Fort Worth, the Brooklyn Museum and the Museum of Contemporary Art in Los Angeles. KAWS lives and works in Brooklyn, New York.
認識植物的神奇世界|Green: The Story of Plant Life on Our Planet
陽光下,樹木靜靜矗立。但是它可不像外在看來那樣悠閒。樹可是忙得很……。這本書要帶領讀者回到地球上開始出現植物的時候,看植物是怎麼進化成樹木,並認識植物的神奇世界。
A magnificent look at the science of plants from the internationally bestselling and multi award-winning team behind Tiny, Lots and Grow.
生活好物 | 編輯精選
杏仁粉+隨行杯果汁機|【林銀杏】母親節寵愛禮盒B款-芝杏經典禮盒

📣限時活動📣即日起下單贈
🎁粮芽棒共享盒 南瓜藜麥口味-168g壹盒
母親節寵愛禮盒B款-芝杏經典禮盒
💖100%天然杏仁研磨製成|給媽媽滿滿的愛🌷💖
🔹精選美國大杏仁,帶皮研磨細緻粉末
🔹不添加奶精、香精、防腐劑以及化學添加物
✔B款-芝杏經典禮盒
經典杏仁粉*2
經典杏仁粉(甜)*2
經典黑芝麻杏仁粉*2
KINYO隨行杯果汁機*1
Driver咖啡豆匙*1
誠品下單獨家贈品-粮芽棒共享盒 南瓜藜麥口味-168g壹盒
時尚選物 | 超值登場
煥膚保濕淨透明亮|綠藤生機無酸煥膚保濕組

新品上市首周熱銷破千支!新客推薦組
煥膚 x 保濕,實證淨透明亮
針對毛孔、粉刺、暗沉等肌膚問題,以獨特「三重煥膚機制」由內而外調理,從源頭中斷毛孔堵塞的惡性循環,三方實證使用 28 天 100% 細緻毛孔、86% 減少粉刺、81% 減少痘痘。
搭配最受新客歡迎、只有 12 個純粹成分的純粹保濕精華液,組成「荷包蛋保養法」,2 步驟高效補水、深入調理油脂與角質,達成淨透明亮的美好膚況。
✔罕見 0% 酸,敏感肌、醫美術後肌、孕婦皆能天天早晚使用。
✔特別推薦給推薦混合到油性肌的朋友。
使肌膚細緻光滑有彈性|ORIGINS品木宣言毛孔救星潔顏組

『泥娃娃活性碳潔顏露』添加同系列經典成分活性碳,磁鐵般的神奇吸力深層吸附100倍的毛孔裡的環境污染毒素、髒污、多餘油脂,徹底淨化,由再搭配經典泥娃娃面膜,讓肌膚更細緻光滑有彈性,黑頭掰掰毛孔白白,以無瑕美肌迎戰夏天!
【抗痘調理】 添加水楊酸,溫和有效煥膚,去除老廢角質,改善毛孔阻塞,防止粉刺生成。有效預防痘痘,毛孔細緻,膚質更平滑
【毛孔深清】 添加「天然黑鑽石」活性碳,磁鐵般的神奇吸力深層吸附環境污染毒素、髒污,毛孔徹底淨化
贈品牌眼鏡包|Overcorrection/ 太陽眼鏡/ OCEB01/琥珀

• Overcorrection無風格限制、無性別限制、無年齡限制、簡單生活,經典時尚。
• 使用"polarized 偏光鏡片",有效消除強反射光線及散色光,使光線變得柔和、景物更自然清晰。
• 墨鏡片拍攝因光線角度而有不同色澤,請以實品顏色為主。
• 墨鏡鏡鏡片皆有抗 UV400 功能
• 符合本標準總號:CNS15067
• 合格檢測指定代碼:D56123